Реклама на сайті газети «Передмістя»
Рекламно-інформаційний портал «Передмістя» містить в собі багато актуальної та цікавої інформації. До Вашої уваги, ми пропонуємо, ознайомитись з усіма рубриками, що представлені на сайті газети і вибрати найбільш підходящу для Вас
На порталі розміщено оголошення про купівлю або продаж товарів і послуг, «Каталог организацій» – де розміщені фірми, компанії всієї України.
Додатковою послугою порталу служить розміщення саме Вашої фірми або організації у нас на сайті. Для цього достатньо зареєструватися на сайті і особистий кабінет у Вашому розпорядженні. Додати або редагувати інформацію, розмістити вакансію або нову подію на порталі та багато інших функціоналів представлено нашим клієнтам в особистому кабінеті.
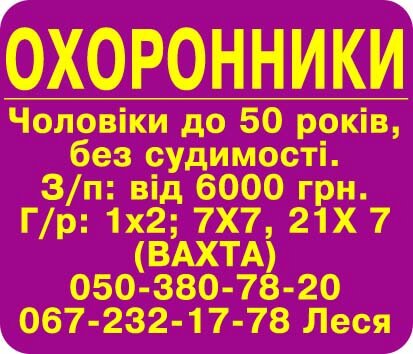
Детальніше ознайомитись з публікацією реклами в газеті, розмістити рекламу на білбордах або на сайті, в рубриці «Розміщення реклами».
Одним із основних напрямків газети служить рубрика «Міськдовідка», – вона містить інформацію по всіх містах Київської області. По кожному місту розписані навчальні заклади, лікарні, комунальні підприємства, телефони екстрених служб і багато іншої корисної інформації, що може знадобитися в повсякденному житті.
Інформація на сайті оновлюється щодня, ми працюємо для Вас. Кожен день сповнений подій, які не можна пропустити, і ми максимальним об’ємом надаємо інформацію на сайт газети «Передмістя».